
Using 500-220 dumps can help you successfully pass the Cisco ECMS certification exam on your first attempt.
Because 500-220 dumps have many success advantages:
- Lightweight Learning Tool (PDF+VCE)
- More free usage time (365 days Free Update)
- Covers all Cisco ECMS practical exam questions and answers, with explanations of difficult problems
- Have a professional Cisco technical team service
So why not use 500-220 dumps to help you easily and successfully pass the exam? And leads4pass, as the provider of 500-220 dumps, has many years of industry reputation, is the industry leader, and is trustworthy, what else do you have to worry about?
Therefore, it is strongly recommended that you use the 500-220 dumps exam material https://www.leads4pass.com/500-220.html, which is up to date throughout the year, to prepare you for a career leap.
More detailed 500-220 ECMS certification information:
Vendor: Cisco
Exam Code: 500-220
Exam Name: Cisco Meraki Solutions Specialist
Certification: Cisco Meraki Solutions Specialist
Duration: 90 minutes
Languages: English
Price: $300 USD
Number of Questions: 55-65
500-220 dumps: https://www.leads4pass.com/500-220.html (Total Questions: 57 Q&A)
Cisco 500-220 exam questions online practice test:
Tips: Verify the answer at the end of the article
Question 1:
When an SSID is configured with the Sign-On Splash page enabled, which two settings must be configured for unauthenticated clients to have full network access and not be allowed listed? (Choose two.)
A. Controller disconnection behavior
B. Captive Portal strength
C. Simultaneous logins
D. Firewall and traffic shaping
E. RADIUS for splash page settings
Question 2:
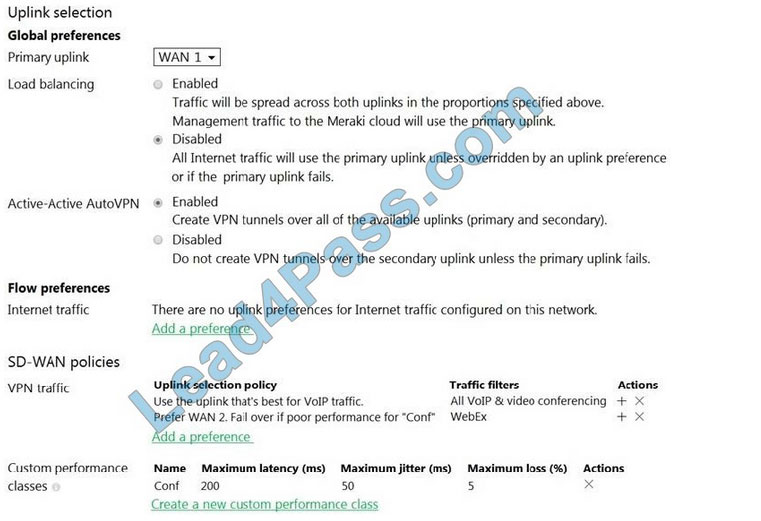
Refer to the exhibit. Assuming this MX has established a full tunnel with its VPN peer, how will the MX route the WebEx traffic?
A. WebEx traffic will prefer WAN 2 as long as it meets the thresholds in the “Conf” performance class.
B. WebEx traffic will prefer WAN 1 as it is the primary uplink.
C. WebEx traffic will prefer WAN 2 as long as it is up.
D. WebEx traffic will be load-balanced between both active WAN links.
Question 3:
For which two reasons can an organization become “Out of License”? (Choose two.)
A. licenses that are in the wrong network
B. more hardware devices than device licenses
C. expired device license
D. licenses that do not match the serial numbers in the organization
E. MR licenses that do not match the MR models in the organization
Question 4:
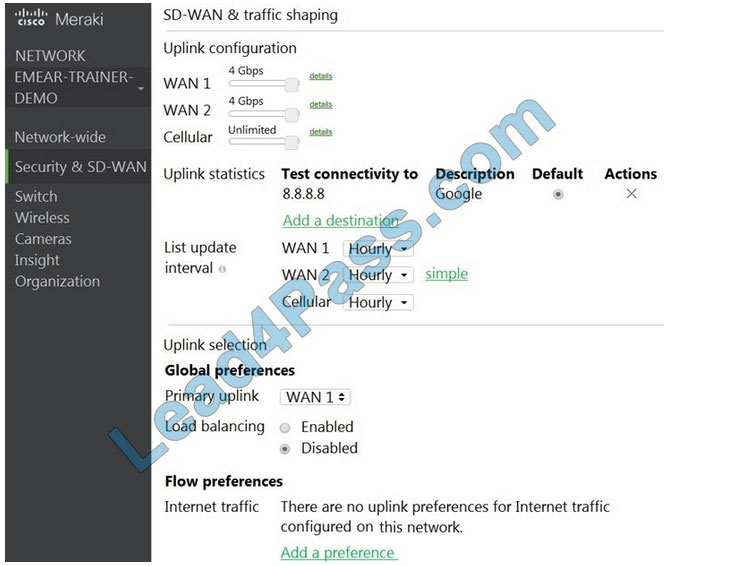
Refer to the exhibit. Which two actions are required to optimize load balancing asymmetrically with a 4:1 ratio between links? (Choose two.)
A. Change the primary uplink to “none”.
B. Add an internet traffic preference that defines the load-balancing ratio as 4:1.
C. Enable load balancing.
D. Set the speed of the cellular uplink to zero.
E. Change the assigned speeds of WAN 1 and WAN 2 so that the ratio is 4:1.
Question 5:
Which Cisco Meraki best practice method preserves complete historical network event logs?
A. Configuring the preserved event number to maximize logging.
B. Configuring the preserved event period to unlimited.
C. Configuring a Syslog server for the network.
D. Configuring Dashboard logging to preserve only certain event types.
Question 6:
Which design requirement is met by implementing Syslog versus SNMP?
A. when automation capabilities are needed
B. when proactive alerts for critical events must be generated
C. when organization-wide information must be collected
D. when information such as flows and client connectivity must be gathered
Question 7:

Refer to the exhibit. The VPN concentrator is experiencing issues. Which action should be taken to ensure a stable environment?
A. Add a deny any/any firewall rule to the end of the firewall rules.
B. Remove the connection from Internet 1.
C. Physically disconnect all LAN ports.
D. Configure the MX appliance to Routed Mode on the Addressing and VLANS page.
Question 8:
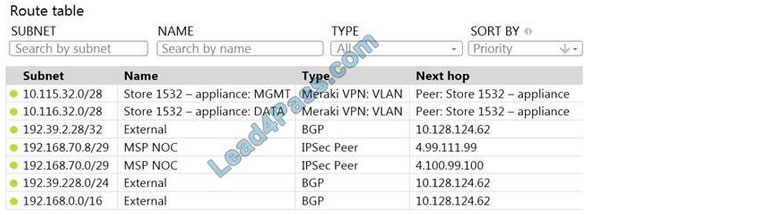
Refer to the exhibit. A packet arrives on the VPN concentrator with source IP 10.168.70.3 and destined for IP 10.116.32.4.
What is the next hop for the packet, based on this concentrator routing table?
A. The concentrator gateway (10.128.124.62) is the next hop.
B. Not enough detail is available to determine the next hop.
C. The packet is stopped.
D. The Auto VPN peer “Store 1532 ? appliance” is the next hop.
Question 9:
Company iPads are enrolled in Systems Manager without supervision, and profiles are pushed through Systems Manager.
Which outcome occurs when a user attempts to remove the “Meraki Management” profile on an iPad?
A. The “Meraki Management” profile cannot be removed.
B. The “Meraki Management” profile is removed and then pushed automatically by the Systems Manager.
C. The “Meraki Management” profile is removed. All the profiles that Systems Manager pushed are also removed.
D. The “Meraki Management” profile is removed. All the profiles Systems Manager pushed remain.
Question 10:
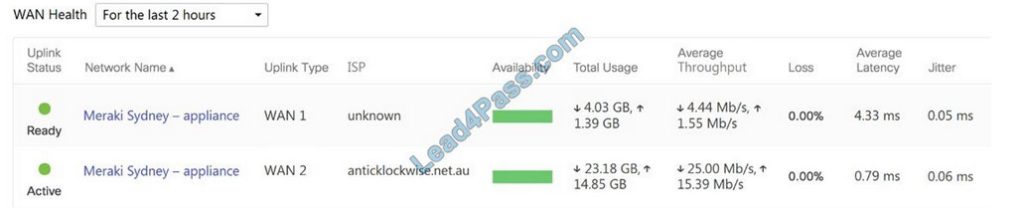
Refer to the exhibit. What are the Loss and Average Latency statistics based on?
A. responses that the MX appliance receives on the connectivity-testing hostnames on the Insight > Web App Health page
B. responses that the MX appliance receives on the connectivity-testing IP addresses on the Security and SD-WAN > Firewall page
C. responses that the MX appliance receives on the connectivity-testing IP address that is configured on the Security and SD-WAN > SD-WAN and Traffic Shaping page
D. responses that the MX appliance receives on the connectivity-testing IP addresses on the Help > Firewall info page
Question 11:
In an organization that uses the Co-Termination licensing model, which two operations enable licenses to be applied? (Choose two.)
A. Renew the Dashboard license.
B. License a network.
C. License more devices.
D. Call Meraki support.
E. Wait for the devices to auto-renew.
Question 12:
Which two Systems Manager Live tools are available only for Apple Macs and Windows PCs and cannot be used on iOS or Android mobile devices? (Choose two.)
A. OS updates
B. Send notification
C. Selective wipe
D. Screenshot
E. Remote Desktop
Question 13:
What are two ways peers interact with ports that Auto VPN uses? (Choose two.)
A. For IPsec tunneling, peers use high UDP ports within the 32768 to 61000 range.
B. Peers contact the VPN registry at UDP port 9350.
C. For IPsec tunneling, peers use high TCP ports within the 32768 to 61000 range.
D. Peers contact the VPN registry at TCP port 9350.
E. For IPsec tunneling, peers use UDP ports 500 and 4500.
Question 14:
What occurs when a configuration change is made to an MX network that is bound to a configuration template?
A. The configuration change in the bound network is combined with the template configuration inside the template.
B. The more restrictive configuration is preferred.
C. The configuration change in the bound network overrides the template configuration.
D. The template configuration overrides the configuration change in the bound network.
Question 15:
One thousand concurrent users stream video to their laptops. A 30/70 split between 2.4 GHz and 5 GHz is used. Based on client count, how many APs (rounded to the nearest whole number) are needed?
A. 26
B. 28
C. 30
D. 32
……
Verify answer:
| Numbers: | Q1 | Q2 | Q3 | Q4 | Q5 | Q6 | Q7 | Q8 | Q9 | Q10 | Q11 | Q12 | Q13 | Q14 | Q15 |
| Answers: | AB | B | BC | BC | A | D | C | B | C | B | AC | CE | BC | A | C |
Cisco Meraki Solutions Specialist certification is a special certification that belongs to the Cisco Meraki Certification and is the only certification.
500-220 ECMS certification exam tests a candidate’s knowledge and skills to engineer Meraki solutions including cloud management, design, implementing, monitoring, and troubleshooting.
Select leads4pass 500-220 dumps https://www.leads4pass.com/500-220.html, Helping you 100% pass the Cisco 500-220 ECMS certification exam.