The latest Oracle 1z0-1072-20 dumps by leads4pass helps you pass the 1z0-1072-20 exam for the first time! leads4pass Latest Update Oracle 1z0-1072-20 VCE Dump and 1z0-1072-20 PDF Dumps, leads4pass 1z0-1072-20 Exam Questions Updated, Answers corrected! Get the latest leads4pass 1z0-1072-20 dumps with Vce and PDF: https://www.leads4pass.com/1z0-1072-20.html (Q&As: 239 dumps)
[Free 1z0-1072-20 PDF] Latest Oracle 1z0-1072-20 Dumps PDF collected by leads4pass Google Drive:
https://drive.google.com/file/d/1M-q5nrHL-5RFYpJl5jDJJZzCzKEXMdg_/
[leads4pass 1z0-1072-20 Youtube] Oracle 1z0-1072-20 Dumps can be viewed on Youtube shared by leads4pass
Latest Oracle 1z0-1072-20 Exam Practice Questions and Answers
QUESTION 1
You are about to upload log file (5 TiB size) to Oracle Cloud Infrastructure object storage and have decided to use
multipart upload capability for a more efficient and resilient upload. Which two statements are true about multipart
upload? (Choose two.)
A. Individual object parts can be as small as 10 MiB or as large as 50 GiB
B. While a multipart upload is still active, you cannot add parts even if the total number of parts is less than 10,000
C. The maximum size for an uploaded object is 10 TiB
D. You do not have to commit the upload after you have uploaded all the object parts
Correct Answer: AC
With multipart upload, you split the object you want to upload into individual parts. Individual parts can be as large as 50
GiB or as small as 10 MiB. (Object Storage waives the minimum part size restriction for the last uploaded part.) Decide
what part number you want to use for each part. Part numbers can range from 1 to 10,000. You do not need to assign
contiguous numbers, but Object Storage constructs the object by ordering part numbers in ascending order. The
maximum size for an uploaded object is 10 TiB While a multipart upload is still active, you can keep adding parts as long
as the total number is less than 10,000. https://docs.cloud.oracle.com/enus/iaas/Content/Object/Tasks/usingmultipartuploads.htm
QUESTION 2
What is the maximum number of security lists that can be associated with a subnet?
A. four
B. three
C. five
D. two
Correct Answer: C
you may optionally specify one or more security lists for the subnet to use (up to five). If you don\\’t specify any, the
subnet uses the cloud network\\’s default security list. You can change which security list the subnet uses at any time.
https://docs.cloud.oracle.com/iaas/Content/Network/Tasks/managingVCNs.htm
QUESTION 3
You have five different company locations spread across the US. For a proof-of-concept (POC) you need to set up
secure and encrypted connection to your workloads running in a single virtual cloud network (VCN) in the Oracle
Cloud
Infrastructure Ashburn region from all company locations.
What would meet this requirement?
A. Create five internet gateways in your VCN and have a separate route table for each internet gateway.
B. Create five virtual circuits using FastConnect for each company location and terminate those connections on a single
dynamic routing gateway (DRG). Attach that DRG to your VCN.
C. Create five IPsec connections with each company location and terminate those connections on a single DRG. Attach
that DRG to your VCN.
D. Create five IPsec VPN connections with each company location and terminate those connections on five separate
DRGs. Attach those DRGs to your VCN.
Correct Answer: C
Access to Your On-Premises Network
There are two ways to connect your on-premises network to Oracle Cloud Infrastructure:
VPN Connect: Offers multiple IPSec tunnels between your existing network\\’s edge and your VCN, by way of a DRG
that you create and attach to your VCN.
Oracle Cloud Infrastructure FastConnect: Offers a private connection between your existing network\\’s edge and Oracle
Cloud Infrastructure. Traffic does not traverse the internet. Both private peering and public peering are supported. That
means your on-premises hosts can access private IPv4 addresses in your VCN as well as regional public IPv4
addresses in Oracle Cloud Infrastructure (for example, Object Storage or public load balancers in your VCN).
You can use one or both types of preceding connections. If you use both, you can use them simultaneously, or in a
redundant configuration. These connections come to your VCN by way of a single DRG that you create and attach to
your
VCN. Without that DRG attachment and a routing rule for the DRG, traffic does not flow between your VCN and on-premises network. At any time, you can detach the DRG from your VCN but maintain all the remaining components that
form
the rest of the connection. You could then reattach the DRG again, or attach it to another VCN.
QUESTION 4
For what business need should you use Database Cloud Service (DBCS) instead of Oracle database on a compute
instance?
A. to bring your own license on a compute service
B. to lower license and infrastructure cost
C. to implement Oracle RAC for high availability
D. to build an Oracle database on a compute service
Correct Answer: C
QUESTION 5
Which two statements about fault domains are true? (Choose two.)
A. A fault domain is a grouping of hardware and infrastructure within an availability domain
B. Each availability domain contains three fault domains
C. A failed instance in a fault domain is automatically relaunched
D. A fault domain is selected automatically based on usage data
Correct Answer: AB
References:
A fault domain is a grouping of hardware and infrastructure within an availability domain. Each availability domain
contains three fault domains. Fault domains provide anti-affinity: they let you distribute your instances so that the
instances are
not on the same physical hardware within a single availability domain.
QUESTION 6
Your customer is using an Oracle Cloud Infrastructure (OCI) compartment named Production that hosts
several resources such as compute instances, DB Systems, and File Systems. Each resource in the Production
compartment is tagged.
The customer\\’s security team wants to restrict access to DB Systems to only the authorized group of DBAs.
Which OCI Tagging capability can be used to meet this requirement?
A. Tags Defaults with predefined values
B. Tag Defaults
C. Cost-Tracking Tags
D. Tag-based Access Control
Correct Answer: D
Reference:
https://docs.cloud.oracle.com/en-us/iaas/Content/Tagging/Tasks/managingaccesswithtags.htm#about
QUESTION 7
Which storage would you use if your big data workload requires shared access and an NFS based interface?
A. File Storage
B. Storage Software Cloud Appliance
C. Object Storage
D. Archive Storage
E. Block Volume
Correct Answer: A
References:
https://docs.cloud.oracle.com/iaas/Content/File/Concepts/filestorageoverview.htm The File Storage service is designed
to meet the needs of applications and users that need an enterprise file system across a wide range of use cases,
including the following:
General Purpose File Storage: Access to an unlimited pool of file systems to manage the growth of structured and
unstructured data.
Big Data and Analytics: Run analytic workloads and use shared file systems to store persistent data. Lift and Shift of
Enterprise Applications: Migrate existing Oracle applications that need NFS storage, such as Oracle E-Business Suite
and
PeopleSoft.
Databases and Transactional Applications: Run test and development workloads with Oracle, MySQL, or other
databases.
Backups, Business Continuity, and Disaster Recovery: Host a secondary copy of relevant file systems from on-premises
to the cloud for backup and disaster recovery purposes. MicroServices and Docker: Deliver stateful persistence for
containers. Easily scale as your container-based environments grow.
QUESTION 8
You created a public subnet and an internet gateway in your virtual cloud network (VCN) of Oracle Cloud Infrastructure.
The public subnet has an associated route table and security list. However, after creating several compute instances In
the public subnet, none can reach the Internet. Which two are possible reasons for the connectivity Issue?
A. A NAT gateway is needed to enable the communication flow to the internet.
B. There Is no stateful egress rule In the security list associated with the public subnet.
C. There Is no dynamic routing gateway (DRG) associated with the VCN.
D. The route table has no default route for routing traffic to the internet gateway.
E. There is no stateful ingress rule in the security list associated with the public subnet.
Correct Answer: BD
QUESTION 9
Which two statements are true about policies?
A. You can use read, write, manage, and inspect as verbs for defining a policy.
B. A policy is a document that specifies who can access which Oracle Cloud Infrastructure resources that your company
has, and how.
C. Users need not do anything but still have to be added to a group with appropriate policies defined.
D. You can deny access to a group via policies.
Correct Answer: BC
QUESTION 10
You have been tasked with creating one virtual cloud network (VCN) each for two lines of business (LOB) applications.
LOB A and LOB B will need to communicate with each other. To ensure that you can utilize VCN peering, which
network CIDR ranges should be used?
A. VCN A (10.0.0.0/16) and VCN B (10.1.0.0/16)
B. VCN A (10.0.2.0/16) and VCN B (10.0.2.0/25)
C. VCN A (10.0.0.0/16) and VCN B (10.0.16.0/24)
D. VCN A (172.16.0.0/24) and VCN B (172.16.0.0/28)
Correct Answer: A
VCN A (10.0.0.0/16) will use a range of IPS from 10.0.0.0 to 10.0.255.255 and VCN B (10.1.0.0/16) will use a range of
IPS from 10.1.0.0 to 10.1.255.255 so will not be any Overlap between 2 VCNs
QUESTION 11
You are asked to create a user that will access programmatic endpoints in Oracle Cloud Infrastructure. The user must
not be allowed to authenticate by username and password. Which two authentication options can you use? (Choose
two.)
A. PEM Certificate file
B. Auth tokens
C. API signing key
D. Windows password
E. SSH key pair
Correct Answer: BC
QUESTION 12
Your application front end consists of several Oracle Cloud Infrastructure compute instances behind a public load
balancer. You have configured the load balancer to perform health checks on these instances. What will happen if an
instance fails to pass the configured health checks?
A. The instance is replaced automatically by the load balancer.
B. The instance is terminated automatically by the load balancer.
C. The instance is taken out of the back end set by the load balancer.
D. The load balancer stops sending traffic to that instance.
Correct Answer: D
One or more of the backend servers reports as unhealthy. A backend server might be unhealthy or the health check
might be misconfigured.
QUESTION 13
You are designing a lab exercise for your team that has a large number of graphics with large file sizes. The application
becomes unresponsive if the graphics are embedded in the application. You have uploaded the graphics to Oracle
Cloud
Infrastructure and only added the URL in the application. You need to ensure these graphics are accessible without
requiring any authentication for an extended period of time.
How can you achieve these requirements?
A. Create pre-authenticated requests (PAR) and specify 00:00:0000 as the expiration time.
B. Make the object storage bucket private and all objects public and use the URL found in the Object “Details”.
C. Make the object storage bucket public and use the URL found in the Object “Details”.
D. Create PARs and do not specify an expiration date.
Correct Answer: C
Pre-authenticated requests provide a way to let you access a bucket or an object without having your own credentials.
For example, you can create a request that lets you upload backups to a bucket without owning API keys.
When you create a bucket, the bucket is considered a private bucket, and access to the bucket and bucket contents
requires authentication and authorization. However, Object Storage supports anonymous, unauthenticated access to a
bucket. You make a bucket public by enabling read access to the bucket.
pre-authenticated requests have to select an expiration date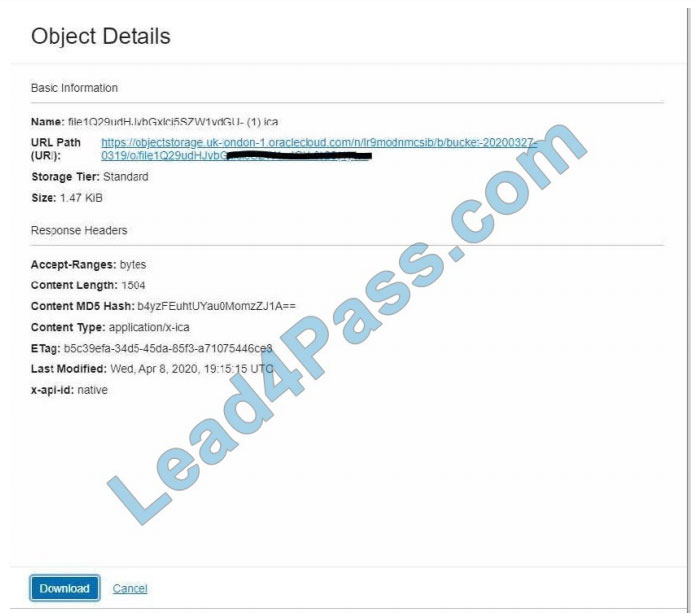
latest updated Oracle 1z0-1072-20 exam questions from the leads4pass 1z0-1072-20 dumps! 100% pass the 1z0-1072-20 exam! Download leads4pass 1z0-1072-20 VCE and PDF dumps: https://www.leads4pass.com/1z0-1072-20.html (Q&As: 239 dumps)
Get free Oracle 1z0-1072-20 dumps PDF online: https://drive.google.com/file/d/1M-q5nrHL-5RFYpJl5jDJJZzCzKEXMdg_/