The latest Amazon DVA-C01 dumps by leads4pass helps you pass the DVA-C01 exam for the first time! leads4pass
Latest Update Amazon DVA-C01 VCE Dump and DVA-C01 PDF Dumps, leads4pass DVA-C01 Exam Questions Updated, Answers corrected!
Get the latest leads4pass DVA-C01 dumps with Vce and PDF: https://www.leads4pass.com/aws-certified-developer-associate.html (Q&As: 454 dumps)
[Free DVA-C01 PDF] Latest Amazon DVA-C01 Dumps PDF collected by leads4pass Google Drive:
https://drive.google.com/file/d/11OBUmZFx83QTWp8sN7IbHUQSZZtKejEY/
[leads4pass DVA-C01 Youtube] Amazon DVA-C01 Dumps can be viewed on Youtube shared by leads4pass
Latest Amazon DVA-C01 Exam Practice Questions and Answers
QUESTION 1
A Developer has created an S3 bucket s3://mycoolapp and has enabled server across logging that points to the folder
s3://mycoolapp/logs. The Developer moved 100 KB of Cascading Style Sheets (CSS) documents to the folder s3://
mycoolapp/css, and then stopped work. When the developer came back a few days later, the bucket was 50 GB.
What is the MOST likely cause of this situation?
A. The CSS files were not compressed and S3 versioning was enabled.
B. S3 replication was enabled on the bucket.
C. Logging into the same bucket caused exponential log growth.
D. An S3 lifecycle policy has moved the entire CSS file to S3 Infrequent Access.
Correct Answer: C
Refer AWS documentation – S3 Server logs
To turn on log delivery, you provide the following logging configuration information: The name of the target bucket where
you want Amazon S3 to save the access logs as objects. You can have logs delivered to any bucket that you own that is
in the same Region as the source bucket, including the source bucket itself. We recommend that you save access logs
in a different bucket so that you can easily manage the logs. If you choose to save access logs in the source bucket, we
recommend that you specify a prefix for all log object keys so that the object names begin with a common string and the
log objects are easier to identify. When your source bucket and target bucket are the same buckets, additional logs are
created for the logs that are written to the bucket. This behavior might not be ideal for your use case because it could
result in a small increase in your storage billing. In addition, the extra logs about logs might make it harder to find the log
that you\\’re looking for.
QUESTION 2
A company is developing an application that will be accessed through the Amazon API Gateway REST API Registered
users should be the only ones who can access certain resources of this API. The token being used should expire
automatically and needs to be refreshed periodically.
How can a developer meet these requirements\\’?
A. Create an Amazon Cognito identity pool, configure the Amazon Cognito Authorizer in API Gateway, and use the
temporary credentials generated by the identity pool
B. Create and maintain a database record for each user with a corresponding token and use an AWS Lambda
authorizer m API Gateway
C. Create an Amazon Cognito user pool, configure the Cognito Authorizer in API Gateway, and use the identity or
access token
D. Create an IAM user for each API user, attach an invoke permissions policy to the API. and use an IAM authorizer in
API Gateway.
Correct Answer: C
Reference: https://aws.amazon.com/premiumsupport/knowledge-center/cognito-custom-scopes-api-gateway/
QUESTION 3
A Developer has set up an Amazon Kinesis Stream with 4 shards to ingest a maximum of 2500 records per second. A
Lambda function has been configured to process these records. In which order will these records be processed?
A. Lambda will receive each record in the reverse order it was placed into the stream following a LIFO (last-in, first-out)
method
B. Lambda will receive each record in the exact order it was placed into the stream following a FIFO (first-in, first-out)
method.
C. Lambda will receive each record in the exact order it was placed into the shard following a FIFO (first-in, first-out)
method. There is no guarantee of order across shards.
D. The Developer can select FIFO, (first-in, first-out), LIFO (last-in, last-out), random, or request specific record using
the getRecords API.
Correct Answer: C
QUESTION 4
A Developer must re-implement the business logic for an order fulfillment system. The business logic has to make
requests to multiple vendors to decide where to purchase an item. The whole process can take up to a week to
complete. What is the MOST efficient and SIMPLEST way to implement a system that meets these requirements?
A. Use AWS Step Functions to execute parallel Lambda functions, and join the results.
B. Create an AWS SQS for each vendor, poll the queue from a worker instance, and joint the results.
C. Use AWS Lambda to asynchronously call a Lambda function for each vendor, and join the results.
D. Use Amazon CloudWatch Events to orchestrate the Lambda functions.
Correct Answer: A
https://aws.amazon.com/step-functions/
QUESTION 5
A Developer accesses AWS CodeCommit over SSH. The SSH keys configured to access AWS CodeCommit are tied to
a user with the following permissions: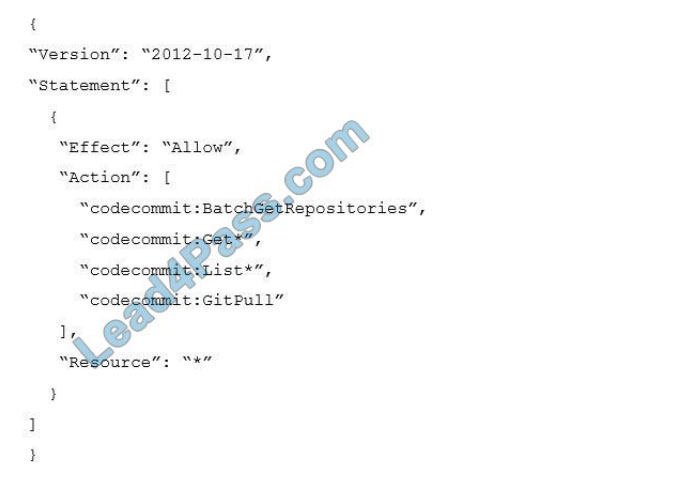
The Developer needs to create/delete branches.
Which specific IAM permissions need to be added, based on the principle of least privilege?
A. “codecommit:CreateBranch””codecommit:DeleteBranch”
B. “codecommit:Put*”
C. “codecommit:Update*”
D. “codecommit:*”
Correct Answer: A
https://docs.aws.amazon.com/codecommit/latest/userguide/auth-and-access-control-permissions-reference.html#aabranches https://docs.aws.amazon.com/codecommit/latest/userguide/auth-and-access-control-iam-identity-basedaccess-control.html
QUESTION 6
A Developer created a Lambda function for a web application backend. When testing the Lambda function from the
AWS Lambda console, the Developer can see that the function is being executed, but there is no log data being
generated in Amazon CloudWatch Logs, even after several minutes.
What could cause this situation?
A. The Lambda function does not have any explicit log statements for the log data to send it to CloudWatch Logs.
B. The Lambda function is missing CloudWatch Logs as a source trigger to send log data.
C. The execution role for the Lambda function is missing permissions to write log data to the CloudWatch Logs.
D. The Lambda function is missing a target CloudWatch Log group.
Correct Answer: C
https://docs.aws.amazon.com/lambda/latest/dg/lambda-monitoring.html
QUESTION 7
An on-premises application is implemented using a Linux, Apache, MySQL, and PHP (LAMP) stack. The Developer
wants to run this application in AWS.
Which of the following sets of AWS services can be used to run this stack?
A. Amazon API Gateway, Amazon S3
B. AWS Lambda, Amazon DynamoDB
C. Amazon EC2, Amazon Aurora
D. Amazon Cognito, Amazon RDS
E. Amazon ECS, Amazon EBS
Correct Answer: C
QUESTION 8
A Developer is trying to deploy a serverless application using AWS CodeDeploy. The application was updated and
needs to be redeployed. What file does the Developer need to update to push that change through CodeDeploy?
A. dockerrun.aws.json
B. buildspec.yml
C. appspec.yml
D. extensions.config
Correct Answer: C
https://docs.aws.amazon.com/codedeploy/latest/userguide/application-revisions-push.html
QUESTION 9
A global company has an application running on Amazon EC2 instances that serves image files from Amazon S3. User
requests from the browser are causing high traffic, which results in degraded performance. Which optimization solution
should a developer implement to increase application performance?
A. Create multiple prefixes in the S3 bucket to increase the request rate.
B. Create an Amazon ElastiCache cluster to cache and serve frequently accessed items.
C. Use Amazon CloudFront to serve the content of images stored in Amazon S3.
D. Submit a ticket to AWS Support to request a rate limit increase for the S3 bucket.
Correct Answer: C
QUESTION 10
A company has a web application that uses an Amazon Cognito user pool for authentication. The company wants to
create a login page with the company logo. What should a developer do to meet these requirements?
A. Create a hosted user interface in Amazon Cognito and customize it with the company logo
B. Create a login page with the company logo and upload it to Amazon Cognito
C. Create a login page in Amazon API Gateway with the logo and save the link in Amazon Cognito.
D. Upload the logo to the Amazon Cognito app settings and point to the logo on a custom login page
Correct Answer: A
QUESTION 11
An Amazon DynamoDB table uses a Global Secondary Index (GSI) to support read queries. The primary table is written heavy, whereas the GSI is used for reading operations. Looking at Amazon CloudWatch metrics, the Developer notices
that write operations to the primary table are throttled frequently under heavy write activity. However, write capacity units
to the primary table are available and not fully consumed.
Why is the table being throttled?
A. The GSI write capacity units are underprovisioned
B. There are not enough read capacity units on the primary table
C. Amazon DynamoDB Streams is not enabled on the table
D. A large write operation is being performed against another table
Correct Answer: A
https://stackoverflow.com/questions/39582752/do-global-secondary-index-gsi-in-dynamodb-impact-tables-provisioncapacity
QUESTION 12
An application writes items to an Amazon DynamoDB table. As the application scales to thousands of instances, calls to
the DynamoDB API generate occasional ThrottlingException errors. The application is coded in a language incompatible
with the AWS SDK.
How should the error be handled?
A. Add exponential backoff to the application logic
B. Use Amazon SQS as an API message bus
C. Pass API calls through Amazon API Gateway
D. Send the items to DynamoDB through Amazon Kinesis Data Firehose
Correct Answer: A
https://aws.amazon.com/premiumsupport/knowledge-center/throttled-ddb/
SDKs automatically add exponential backoff. If not using the AWS SDKs, add your own backoff logic to the application
code.
https://docs.aws.amazon.com/amazondynamodb/latest/developerguide/Programming.Errors.html#Programming.Errors.
Handling
QUESTION 13
An application running on Amazon EC2 opens connections to an Amazon RDS SQL Server database. The developer
does not want to store the user name and password for the database in the code. The developer would also like to
automatically rotate the credentials.
What is the MOST secure way to store and access the database credentials?
A. Create an IAM role that has permissions to access the database. Attach the role to the EC2 instance.
B. Use AWS Secrets Manager to store the credentials. Retrieve the credentials from Secrets Manager as needed.
C. Store the credentials in an encrypted text file in an Amazon S3 bucket. Configure the EC2 instance\\’s user data to
download the credentials from Amazon S3 as the instance boots.
D. Store the user name and password credentials directly in the source code. No further action is needed because the
source code is stored in a private repository.
Correct Answer: B
Reference: https://aws.amazon.com/blogs/security/rotate-amazon-rds-database-credentials-automatically-with-awssecrets-manager/
latest updated Amazon DVA-C01 exam questions from the leads4pass DVA-C01 dumps! 100% pass the DVA-C01 exam!
Download leads4pass DVA-C01 VCE and PDF dumps: https://www.leads4pass.com/aws-certified-developer-associate.html (Q&As: 454 dumps)
Get free Amazon DVA-C01 dumps PDF online: https://drive.google.com/file/d/11OBUmZFx83QTWp8sN7IbHUQSZZtKejEY/