The latest Amazon SCS-C01 dumps by leads4pass helps you pass the SCS-C01 exam for the first time! leads4pass
Latest Update Amazon SCS-C01 VCE Dump and SCS-C01 PDF Dumps, leads4pass SCS-C01 Exam Questions Updated, Answers corrected!
Get the latest leads4pass SCS-C01 dumps with Vce and PDF: https://www.leads4pass.com/aws-certified-security-specialty.html (Q&As: 358 dumps)
[Free SCS-C01 PDF] Latest Amazon SCS-C01 Dumps PDF collected by leads4pass Google Drive:
https://drive.google.com/file/d/1z0uAmpe44ny341Wj3sMC0fHFRKfvpT9D/
[leads4pass SCS-C01 Youtube] Amazon SCS-C01 Dumps can be viewed on Youtube shared by leads4pass
Latest Amazon SCS-C01 Exam Practice Questions and Answers
QUESTION 1
A recent security audit found that AWS CloudTrail logs are insufficiently protected from tampering and unauthorized
access. Which actions must the Security Engineer take to access these audit findings? (Choose three.)
A. Ensure CloudTrail log file validation is turned on.
B. Configure an S3 lifecycle rule to periodically archive CloudTrail logs into Glacier for long-term storage.
C. Use an S3 bucket with tight access controls that exists in a separate account.
D. Use Amazon Inspector to monitor the file integrity of CloudTrail log files.
E. Request a certificate through ACM and use a generated certificate private key to encrypt CloudTrail log files.
F. Encrypt the CloudTrail log files with server-side encryption AWS KMS-managed keys (SSE-KMS).
Correct Answer: ABF
Reference: https://docs.aws.amazon.com/awscloudtrail/latest/userguide/best-practices-security.html
QUESTION 2
One of your company\\’s EC2 Instances has been compromised. The company has strict po thorough investigation on
finding the culprit for the security breach. What would you do in from the options given below? Please select:
A. Take a snapshot of the EBS volume
B. Isolate the machine from the network
C. Make sure that logs are stored securely for auditing and troubleshooting purpose
D. Ensure all passwords for all 1 AM users are changed
E. Ensure that all access kevs are rotated.
Correct Answer: ABC
Some of the important aspects in such a situation are 1) First isolate the instance so that no further security harm can
occur on other AWS resources 2) Take a snapshot of the EBS volume for further investigation. This is in case if you
need to shut down the initial instance and do a separate investigation on the data 3) Next is Option C. This indicates that
we have already got logs and we need to make sure that it is stored securely so that n unauthorized person can access
it and manipulate it. Options D and E are invalid because they could have adverse effects for the other 1 AM users. For
more information on adopting a security framework, please refer to the below URL https://d1.awsstatic.com/whitepapers/compliance/NIST Cybersecurity Framework
Note:
In the question, we have been asked to take action to find the culprit and to help the investigation or to further reduce
the damage that has happened due to the security breach. So by keeping logs secure is one way of helping the
investigation. The correct answers are: Take a snapshot of the EBS volume. Isolate the machine from the network.
Make sure that logs are stored securely for auditing and troubleshooting purpose Submit your Feedback/Queries to our
Experts
QUESTION 3
A Security Engineer is trying to determine whether the encryption keys used in an AWS service are in compliance with
certain regulatory standards. Which of the following actions should the Engineer perform to get further guidance?
A. Read the AWS Customer Agreement.
B. Use AWS Artifact to access AWS compliance reports.
C. Post the question on the AWS Discussion Forums.
D. Run AWS Config and evaluate the configuration outputs.
Correct Answer: B
QUESTION 4
A corporate cloud security policy states that communications between the company\\’s VPC and KMS must travel
entirely within the AWS network and not use public service endpoints. Which combination of the following actions MOST
satisfies this requirement? (Choose two.)
A. Add the AWS:sourceVpce condition to the AWS KMS key policy referencing the company\\’s VPC endpoint ID.
B. Remove the VPC internet gateway from the VPC and add a virtual private gateway to the VPC to prevent direct,
public internet connectivity.
C. Create a VPC endpoint for AWS KMS with private DNS enabled.
D. Use the KMS Import Key feature to securely transfer the AWS KMS key over a VPN.
E. Add the following condition to the AWS KMS key policy: “AWS: SourceIp”: “10.0.0.0/16”.
Correct Answer: AC
An IAM policy can deny access to KMS except through your VPC endpoint with the following condition statement:
“Condition”: {
“StringNotEquals”: {
“aws:sourceVpce”: “vpce-0295a3caf8414c94a”
}
}
If you select the Enable Private DNS Name option, the standard AWS KMS DNS hostname
(https://kms..amazonaws.com) resolves to your VPC endpoint.
QUESTION 5
Some highly sensitive analytics workloads are to be moved to Amazon EC2 hosts. Threat modeling has found that a risk
exists where a subnet could be maliciously or accidentally exposed to the internet. Which of the following mitigations
should be recommended?
A. Use AWS Config to detect whether an Internet Gateway is added and use an AWS Lambda function to provide auto-remediation.
B. Within the Amazon VPC configuration, mark the VPC as private and disable Elastic IP addresses.
C. Use IPv6 addressing exclusively on the EC2 hosts, as this prevents the hosts from being accessed from the internet.
D. move the workload to a Dedicated Host, as this provides additional network security controls and monitoring.
Correct Answer: B
QUESTION 6
A company wants to use Cloudtrail for logging all API activity. They want to segregate the logging of data events and
management events. How can this be achieved? Choose 2 answers from the options given below Please select:
A. Create one Cloudtrail log group for data events
B. Create one trail that logs data events to an S3 bucket
C. Create another trail that logs management events to another S3 bucket
D. Create another Cloudtrail log group for management events
Correct Answer: BC
The AWS Documentation mentions the following
You can configure multiple trails differently so that the trails process and log only the events that you specify. For
example, one trail can log read-only data and management events, so that all read-only events are delivered to one S3
bucket. Another trail can log only write-only data and management events so that all write-only events are delivered to
a separate S3 bucket Options A and D are invalid because you have to create a trail and not a log group For more
information on managing events with cloud trail, please visit the following URL:
https://docs.aws.amazon.com/awscloudtrail/latest/userguide/loHEing-manasement-and-data-events-with-cloudtrai The
correct answers are: Create one trail that logs data events to an S3 bucket. Create another trail that logs management
events to another S3 bucket Submit your Feedback/Queries to our Experts
QUESTION 7
A Web Administrator for the website example.com has created an Amazon CloudFront distribution for
dev.example.com, with a requirement to configure HTTPS using a custom TLS certificate imported to AWS Certificate
Manager. Which combination of steps is required to ensure the availability of the certificate in the CloudFront console?
(Choose two.)
A. Call UploadServerCertificate with /cloudfront/dev/ in the path parameter.
B. Import the certificate with a 4,096-bit RSA public key.
C. Ensure that the certificate, private key, and certificate chain are PKCS #12-encoded.
D. Import the certificate in the us-east-1 (N. Virginia) Region.
E. Ensure that the certificate, private key, and certificate chain are PEM-encoded.
Correct Answer: BD
QUESTION 8
Your company has an EC2 Instance hosted in AWS. This EC2 Instance hosts an application. Currently, this application
is experiencing a number of issues. Do you need to inspect the network packets to see what type of error that is
occurring? Which one of the below steps can help address this issue?
Please select:
A. Use the VPC Flow Logs.
B. Use a network monitoring tool provided by an AWS partner.
C. Use another instance. Setup a port to “promiscuous mode” and sniff the traffic to analyze the packets.
D. Use Cloudwatch metric
Correct Answer: B
QUESTION 9
Your company has mandated that all data in AWS be encrypted at rest. How can you achieve this for EBS volumes?
Choose 2 answers from the options given below Please select:
A. Use Windows bit locker for EBS volumes on Windows instances
B. Use TrueEncrypt for EBS volumes on Linux instances
C. Use AWS Systems Manager to encrypt the existing EBS volumes
D. Boot EBS volume can be encrypted during launch without using custom AMI
Correct Answer: AB
EBS encryption can also be enabled when the volume is created and not for existing volumes. One can use existing
tools for OS-level encryption.
Option C is incorrect.
AWS Systems Manager is a management service that helps you automatically collect software inventory, apply OS
patches, create system images and configure Windows and Linux operating systems.
Option D is incorrect
You cannot choose to encrypt a non-encrypted boot volume on instance launch. To have encrypted boot volumes
during launch, your custom AMI must have it\\’s boot volume encrypted before launch.
For more information on the Security Best practices, please visit the following URL:
com/whit Security Practices.
The correct answers are: Use Windows bit locker for EBS volumes on Windows instances. Use TrueEncrypt for EBS
volumes on Linux instances
Submit your Feedback/Queries to our Experts
QUESTION 10
Company policy requires that all insecure server protocols, such as FTP, Telnet, HTTP, etc be disabled on all servers.
The security team would like to regularly check all servers to ensure compliance with this requirement by using a
scheduled CloudWatch event to trigger a review of the current infrastructure. What process will check compliance of the
company\\’s EC2 instances?
Please select:
A. Trigger an AWS Config Rules evaluation of the restricted-common-ports rule against every EC2 instance.
B. Query the Trusted Advisor API for all best-practice security checks and check for “action recommended” status.
C. Enable a GuardDuty threat detection analysis targeting the port configuration on every EC2 instance.
D. Run an Amazon inspector assessment using the Runtime Behavior Analysis rules package against every EC2
instance.
Correct Answer: D
Option B is incorrect because querying Trusted Advisor API\\’s are not possible
Option C is incorrect because GuardDuty should be used to detect threats and not check the compliance of security
protocols.
Option D states that Run Amazon Inspector using runtime behavior analysis rules which will analyze the behavior of
your instances during an assessment run, and provide guidance about how to make your EC2 instances more secure.
Insecure Server Protocols
This rule helps determine whether your EC2 instances allow support for insecure and unencrypted ports/services such
as FTP, Telnet HTTP, IMAP, POP version 3, SMTP, SNMP versions 1 and 2, rsh, and rlogin.
For more information, please refer to the below URL:
https://docs.aws.amazon.eom/mspector/latest/userguide/inspector_runtime-behavior-analysis.html#insecure-protocols
(
The correct answer is: Run an Amazon Inspector assessment using the Runtime Behavior Analysis rules package
against every EC2 instance.
Submit your Feedback/Queries to our Experts
QUESTION 11
You have an Amazon VPC that has a private subnet and a public subnet in which you have a NAT instance server. You
have created a group of EC2 instances that configure themselves at startup by downloading a bootstrapping script from
S3 that deploys an application via GIT.
Which one of the following setups would give us the highest level of security?
Choose the correct answer from the options given below.
Please select:
A. EC2 instances in our public subnet, no EIPs, route outgoing traffic via the IGW
B. EC2 instances in our public subnet assigned EIPs, and route outgoing traffic via the NAT
C. EC2 instance in our private subnet assigned EIPs, and route our outgoing traffic via our IGW
D. EC2 instances in our private subnet, no EIPs, route outgoing traffic via the NAT
Correct Answer: D
QUESTION 12
An Application Developer is using an AWS Lambda function that must use AWS KMS to perform encrypt and decrypt
operations for API keys that are less than 2 KB.
Which key policy would allow the application to do this while granting least privilege?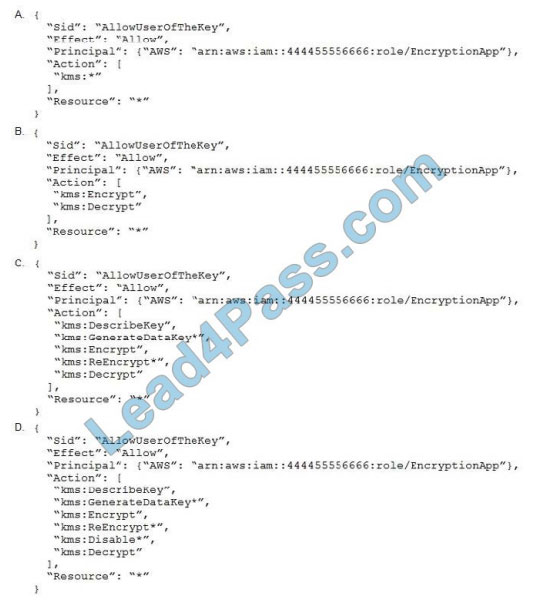
A. Option A
B. Option B
C. Option C
D. Option D
Correct Answer: C
QUESTION 13
Your company has a requirement to monitor all root user activity by notification. How can this best be achieved? Choose
2 answers from the options given below. Each answer forms part of the solution Please select:
A. Create a Cloudwatch Events Rule s
B. Create a Cloudwatch Logs Rule
C. Use a Lambda function
D. Use Cloudtrail API call
Correct Answer: AC
Option B is invalid because you need to create a Cloudwatch Events Rule and there is such thing as a Cloudwatch Logs
Rule Option D is invalid because Cloud Trail API calls can be recorded but cannot be used to send across notifications
For more information on this blog article, please visit the following URL: https://aws.amazon.com/blogs/mt/monitor-andnotify-on-aws-account-root-user-activityy The correct answers are: Create a Cloudwatch Events Rule, Use a Lambda
function Submit your Feedback/Queries to our Experts
latest updated Amazon SCS-C01 exam questions from the leads4pass SCS-C01 dumps! 100% pass the SCS-C01 exam!
Download leads4pass SCS-C01 VCE and PDF dumps: https://www.leads4pass.com/aws-certified-security-specialty.html (Q&As: 358 dumps)
Get free Amazon SCS-C01 dumps PDF online: https://drive.google.com/file/d/1z0uAmpe44ny341Wj3sMC0fHFRKfvpT9D/