
Table Of Content:
- Amazon SCS-C01 Dumps Pdf
- Amazon SCS-C01 Dumps Youtube
- Amazon SCS-C01 Exam Practice Test
- Amazon Discount Code 2021
Share Amazon SCS-C01 exam practice questions and answers from leads4pass latest updated SCS-C01 dumps free of charge. Get the latest uploaded SCS-C01 dumps pdf from google driver online. To get the full Amazon SCS-C01 dumps PDF or dumps VCE visit: https://www.leads4pass.com/aws-certified-security-specialty.html (Q&As: 487). all Amazon SCS-C01 exam questions have been updated, the answer has been corrected!
Make sure your exam questions are real and effective to help you pass your first exam!
[Amazon SCS-C01 Dumps pdf] Latest Amazon SCS-C01 Dumps PDF collected by leads4pass Google Drive:
https://drive.google.com/file/d/1gxjXmimix-Am035QQ2m156IYqyyVMcpa/
[Amazon SCS-C01 Youtube] Amazon SCS-C01 exam questions and answers are shared free of charge from Youtube watching uploads from leads4pass.
Latest Update Amazon SCS-C01 Exam Practice Questions and Answers Online Test
QUESTION 1
Which technique can be used to integrate AWS IAM (Identity and Access Management) with an on-premise LDAP
(Lightweight Directory Access Protocol) directory service?
Please select: A. Use an IAM policy that references the LDAP account identifiers and the AWS credentials.
B. Use SAML (Security Assertion Markup Language) to enable single sign-on between AWS and LDAP.
C. Use AWS Security Token Service from an identity broker to issue short-lived AWS credentials.
D. Use IAM roles to automatically rotate the IAM credentials when LDAP credentials are updated.
Correct Answer: B
On the AWS Blog site, the following information is present to help in this context The newly released whitepaper. Single
Sign-On: Integrating AWS, OpenLDAP, and Shibboleth will help you integrate your existing LDAP-based user directory
with AWS. When you integrate your existing directory with AWS, your users can access AWS by using their existing
credentials. This means that your users don\\’t need to maintain yet another user name and password just to access
AWS resources. Option
A.C and D are all invalid because, in this sort of configuration, you have to use SAML to enable single sign-on.
For more information on integrating AWS with LDAP for Single Sign-On, please visit the following URL:
https://aws.amazon.eom/blogs/security/new-whitepaper-sinEle-sign-on-inteErating-aws-openldap-andshibboleth/
The correct answer is: Use SAML (Security Assertion Markup Language) to enable single sign-on between
AWS and LDAP.
QUESTION 2
A company has set up the following structure to ensure that their S3 buckets always have logging enabled![[2021.4] leads4pass scs-c01 practice test q2](https://www.exammarkers.com/wp-content/uploads/2021/04/q2.jpg)
If there are any changes to the configuration to an S3 bucket, a config rule gets checked. If logging is disabled, then
Lambda function is invoked. This Lambda function will again enable logging on the S3 bucket. Now there is an issue
being encountered with the entire flow. You have verified that the Lambda function is being invoked. But when logging is
disabled for the bucket, the lambda function does not enable it again. Which of the following could be an issue
Please select:
A. The AWS Config rule is not configured properly
B. The AWS Lambda function does not have appropriate permissions for the bucket
C. The AWS Lambda function should use Node.js instead of python.
D. You need to also use the API gateway to invoke the lambda function
Correct Answer: B
The most probable cause is that you have not allowed the Lambda functions to have the appropriate permissions on the
S3 bucket to make the relevant changes. Option A is invalid because this is more of permission instead of a
configuration rule issue. Option C is invalid because changing the language will not be the core solution. Option D is
invalid because you don\\’t necessarily need to use the API gateway service For more information on accessing
resources from a Lambda function, please refer to the below URL https://docs.aws.amazon.com/lambda/latest/ds/accessingresources.htmll The correct answer is: The AWS Lambda function does not have appropriate permissions for the
bucket
QUESTION 3
You need to ensure that objects in an S3 bucket are available in another region. This is because of the criticality of the
data that is hosted in the S3 bucket. How can you achieve this in the easiest way possible?
Please select:
A. Enable cross-region replication for the bucket
B. Write a script to copy the objects to another bucket in the destination region
C. Create an S3 snapshot in the destination region
D. Enable versioning which will copy the objects to the destination region
Correct Answer: A
Option B is partially correct but a big maintenance overhead to create and maintain a script when the functionality is
already available in S3 Option C is invalid because snapshots are not available in S3 Option D is invalid because
versioning will not replicate objects The AWS Documentation mentions the following Cross-region replication is a bucket level configuration that enables automatic, asynchronous copying of objects across buck in different AWS Regions. For
more information on Cross-region replication in the Simple Storage Service, please visit the below URL:
https://docs.aws.amazon.com/AmazonS3/latest/dev/crr.html The correct answer is: Enable cross-region replication for
the bucket
QUESTION 4
In your LAMP application, you have some developers that say they would like access to your logs. However, since you
are using an AWS Auto Scaling group, your instances are constantly being re-created. What would you do to make sure
that these developers can access these log files? Choose the correct answer from the options below
Please select:
A. Give only the necessary access to the Apache servers so that the developers can gain access to the log files.
B. Give root access to your Apache servers to the developers.
C. Give read-only access to your developers to the Apache servers.
D. Set up a central logging server that you can use to archive your logs; archive these logs to an S3 bucket for
developer access.
Correct Answer: D
One important security aspect is to never give access to actual servers, hence Option A.B and C are just totally wrong
from a security perspective. The best option is to have a central logging server that can be used to archive logs. These
logs can then be stored in S3. Options A, B, and C are all invalid because you should not give access to the developers
on the Apache se For more information on S3, please refer to the below link https://aws.amazon.com/documentation/s3
The correct answer is: Set up a central logging server that you can use to archive your logs; archive these logs to an S3
bucket for developer access. Submit your Feedback/Queries to our Experts
QUESTION 5
Which of the following is not a best practice for carrying out a security audit?
Please select:
A. Conduct an audit on a yearly basis
B. Conduct an audit if application instances have been added to your account
C. Conduct an audit if you ever suspect that an unauthorized person might have accessed your account
D. Whenever there are changes in your organization
Correct Answer: A
A year\\’s time is generally too long a gap for conducting security audits The AWS Documentation mentions the
following You should audit your security configuration in the following situations: On a periodic basis. If there are
changes in your organization, such as people leaving. If you have stopped using one or more individual AWS services.
This is important for removing permissions that users in your account no longer need. If you\\’ve added or removed
software in your accounts, such as applications on Amazon EC2 instances, AWS OpsWor stacks, AWS CloudFormation
templates, etc. If you ever suspect that an unauthorized person might have accessed your account. Options B, C, and D
are all the right ways and recommended best practices when it comes to conducting audits For more information on
Security Audit guideline, please visit the below URL: https://docs.aws.amazon.com/eeneral/latest/gr/aws-security-auditeuide.html The correct answer is: Conduct an audit on a yearly basis
QUESTION 6
You have a website that is sitting behind AWS Cloudfront. You need to protect the web site against threats such as
SQL injection and Cross-site scripting attacks. Which of the following service can help in such a scenario
Please select:
A. AWS Trusted Advisor
B. AWS WAF
C. AWS Inspector
D. AWS Config
Correct Answer: B
The AWS Documentation mentions the following AWS WAF is a web application firewall that helps detect and block
malicious web requests targeted at your web applications. AWS WAF allows you to create rules that can help protect
against common web exploits like SQL injection and cross-site scripting. With AWS WAF you first identify the resource
(either an Amazon CloudFront distribution or an Application Load Balancer) that you need to protect. Option A is invalid
because this will only give advice on how you can better the security in your AWS account but not protect against
threats mentioned in the question. Option C is invalid because this can be used to scan EC2 Instances for vulnerabilities
but not protect against threats mentioned in the question. Option D is invalid because this can be used to check config
changes but not protect against threats mentioned in the quest For more information on AWS WAF, please visit the
following URL: https://aws.amazon.com/waf/details; The correct answer is: AWS WAF
QUESTION 7
A security engineer is designing a solution that will provide end-to-end encryption between clients and Docker
containers running In Amazon Elastic Container Service (Amazon ECS). This solution will also handle volatile traffic
patterns
Which solution would have the MOST scalability and LOWEST latency?
A. Configure a Network Load Balancer to terminate the TLS traffic and then re-encrypt the traffic to the containers
B. Configure an Application Load Balancer to terminate the TLS traffic and then re-encrypt the traffic to the containers
C. Configure a Network Load Balancer with a TCP listener to pass through TLS traffic to the containers
D. Configure Amazon Route 53 to use multivalue answer routing to send traffic to the containers
Correct Answer: A
QUESTION 8
One of your company\\’s EC2 Instances has been compromised. The company has a strict no thorough investigation on
finding the culprit for the security breach. What would you do from the options given below?
Please select:
A. Take a snapshot of the EBS volume
B. Isolate the machine from the network
C. Make sure that logs are stored securely for auditing and troubleshooting purpose
D. Ensure all passwords for all IAM users are changed
E. Ensure that all access keys are rotated.
Correct Answer: ABC
Option C. This indicates that we have already got logs and we need to make sure that it is stored securely so that n
unauthorized person can access it and manipulate it. Options D and E are invalid because they could have adverse
effects for the other IAM users. For more information on adopting a security framework, please refer to the below URL
HTTPS://d1.awsstatic.com/whitepapers/compliance/NIST Cybersecurity Framework Note: In the question, we have been
asked to take actions to find the culprit and to help the investigation or to further reduce the damage that has happened
due to the security breach. So by keeping logs secure is one way of helping the investigation. The correct answers are:
Take a snapshot of the EBS volume. Isolate the machine from the network. Make sure that logs are stored securely for
auditing and troubleshooting purpose
QUESTION 9
A corporation is preparing to acquire several companies. A Security Engineer must design a solution to ensure that
newly acquired AWS accounts follow the corporation\\’s security best practices. The solution should monitor each
Amazon S3 bucket for unrestricted public write access and use AWS managed services.
What should the Security Engineer do to meet these requirements?
A. Configure Amazon Macie to continuously check the configuration of all S3 buckets.
B. Enable AWS Config to check the configuration of each S3 bucket.
C. Set up AWS Systems Manager to monitor S3 bucket policies for public write access.
D. Configure an Amazon EC2 instance to have an IAM role and a cron job that checks the status of all S3 buckets.
Correct Answer: C
QUESTION 10
A company\\’s application runs on Amazon EC2 and stores data in an Amazon S3 bucket The company wants
additional security controls in place to limit the likelihood of accidental exposure of data to external parties
Which combination of actions will meet this requirement? (Select THREE.)
A. Encrypt the data in Amazon S3 using server-side encryption with Amazon S3 managed encryption keys (SSE-S3)
B. Encrypt the data in Amazon S3 using server-side encryption with AWS KMS managed encryption keys (SSE-KMS)
C. Create a new Amazon S3 VPC endpoint and modify the VPC\\’s routing tables to use the new endpoint
D. Use the Amazon S3 Block Public Access feature.
E. Configure the bucket policy to allow access from the application instances only
F. Use an NACL to filter traffic to Amazon S3
Correct Answer: BCE
QUESTION 11
A Security Engineer for a large company is managing a data processing application used by 1,500 subsidiary
companies. The parent and subsidiary companies all use AWS. The application uses TCP port 443 and runs on
Amazon EC2 behind a Network Load Balancer (NLB). For compliance reasons, the application should only be
accessible to the subsidiaries and should not be available on the public internet. To meet the compliance requirements
for restricted access, the Engineer has received the public and private CIDR block ranges for each subsidiary
What solution should the Engineer use to implement the appropriate access restrictions for the application?
A. Create a NaCl to allow access on TCP port 443 from the 1;500 subsidiary CIDR block ranges. Associate the NaCl
to both the NLB and EC2 instances
B. Create an AWS security group to allow access on TCP port 443 from the 1,500 subsidiary CIDR block ranges.
Associate the security group to the NLB. Create a second security group for EC2 instances with access to TCP port
443 from the NLB security group.
C. Create an AWS PrivateLink endpoint service in the parent company account attached to the NLB. Create an AWS
security group for the instances to allow access on TCP port 443 from the AWS PrivateLink endpoint. Use AWS
PrivateLink interface endpoints in the 1,500 subsidiary AWS accounts to connect to the data processing application.
D. Create an AWS security group to allow access on TCP port 443 from the 1,500 subsidiary CIDR block ranges.
Associate the security group with EC2 instances.
Correct Answer: D
QUESTION 12
An Application team has requested a new AWS KMS master key for use with Amazon S3, but the organizational
security policy requires separate master keys for different AWS services to limit the blast radius.
How can an AWS KMS customer master key (CMK) be constrained to work with only Amazon S3?
A. Configure the CMK key policy to allow only the Amazon S3 service to use the KMS Encrypt action
B. Configure the CMK key policy to allow AWS KMS actions only when the KMS ViaService condition matches the
Amazon S3 service name.
C. Configure the IAM user\\’s policy to allow KMS to pass a rote lo Amazon S3
D. Configure the IAM user\\’s policy to allow only Amazon S3 operations when they are combined with the CMK
Correct Answer: B
QUESTION 13
A company hosts multiple externally facing applications, each isolated in its own AWS account The company\\’B
The security team has enabled AWS WAF. AWS Config. and Amazon GuardDuty on all accounts. The company\\’s
The operations team has also joined all of the accounts to AWS Organizations and established centralized logging for
CloudTrail. AWS Config, and GuardDuty. The company wants the Security team to take reactive remediation in one
account, and automate implementing this remediation as proactive prevention in all the other accounts.
How should the Security team accomplish this?
A. Update the AWS WAF rules in the affected account and use AWS Firewall Manager to push updated AWS WAF
rules across all other accounts.
B. Use GuardDuty centralized logging and Amazon SNS to set up alerts to notify all application teams of security
incidents.
C. Use GuardDuty alerts to write an AWS Lambda function that updates all accounts by adding additional NACLs on the
Amazon EC2 instances to block known malicious IP addresses.
D. Use AWS Shield Advanced to identify threats in each individual account and then apply the account-based
protections to all other accounts through Organizations.
Correct Answer: C
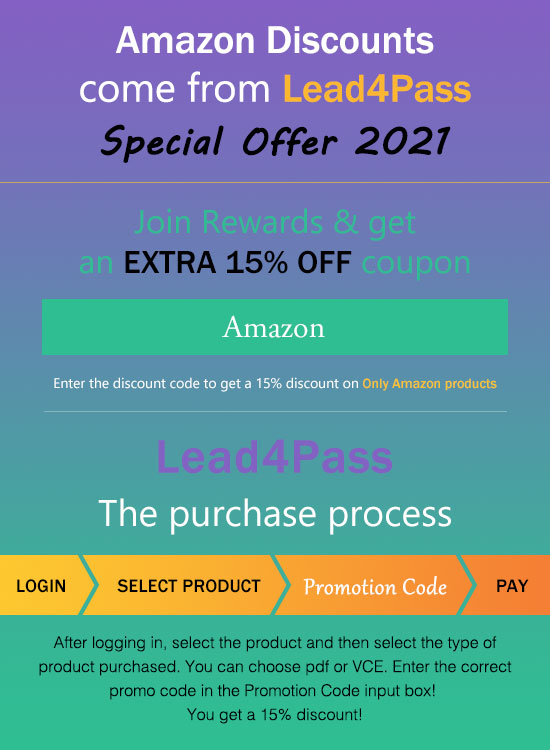
leads4pass Amazon Discount Code 2021
For the full Amazon SCS-C01 exam dumps from leads4pass SCS-C01 Dumps pdf or Dumps VCE visit: https://www.leads4pass.com/aws-certified-security-specialty.html (Q&As: 487 dumps)
ps.
Get free Amazon SCS-C01 dumps PDF online: https://drive.google.com/file/d/1gxjXmimix-Am035QQ2m156IYqyyVMcpa/